The dark web is not powered by a single system but by multiple anonymous networks designed to protect user identity, privacy, and freedom from surveillance. Each dark web network operates differently, offering varying levels of anonymity, security, speed, and accessibility.
Some are widely used for private communication and information sharing, while others are built for censorship resistance or decentralized hosting.
Understanding the different types of dark web networks helps explain how the dark web functions, who uses it, and the risks and benefits associated with each network.
What is the Dark Web? Understanding Its Privacy and Security Risks
Before we explore the various dark web network possibilities, let’s first understand what we mean by the term “dark web” and clear up one of the biggest misunderstandings about it, which is that it’s not just another name for the deep web!
Deep web content is anything that can’t be accessed from a public Internet search without having to provide some kind of authentication to gain access to it (e.g., sending you an email address, your username/password to gain access, etc.).
To illustrate: your inbox with Gmail, your banking via the internet, your medical records, private channels within Slack, and the Subscriptions you have with the services. These all exist, and every day, most people use these, yet none of these things are able to be found via Google by searching for them. These items will not be found anywhere in a search engine.
What is the Dark Web?
The dark web consists of various independent and interconnected networks and websites that serve people who want to remain anonymous or engage in illegal activities, such as the underground economy.
These networks/websites are created using technologies designed specifically to ensure that the user (the consumer) can operate in an anonymous environment. The technology used to encrypt/mask the traffic over a particular site creates an environment that allows for the protection of the user; this anonymity prevents any one person from being able to see or track any activity.
The dark web exists to provide a level of privacy beyond what traditional web browsers or standard encryption methods can offer.
People seek anonymity for many reasons, journalists protect their sources, activists avoid censorship, whistleblowers expose corporate wrongdoing, and researchers communicate under surveillance.
All of these different human behaviors happen at the same time as a variety of illegal and criminal behaviors occur in the same digital space. The two sides to the dark web (the good and bad) make up its complexity and danger; because of that, it’s critical to have a general understanding of the types of dark web networks available, since no two function the same way.
Different users are attracted to various types of dark web networks depending on their level of risk and the function of the dark web network.
Types of Dark Web Networks?
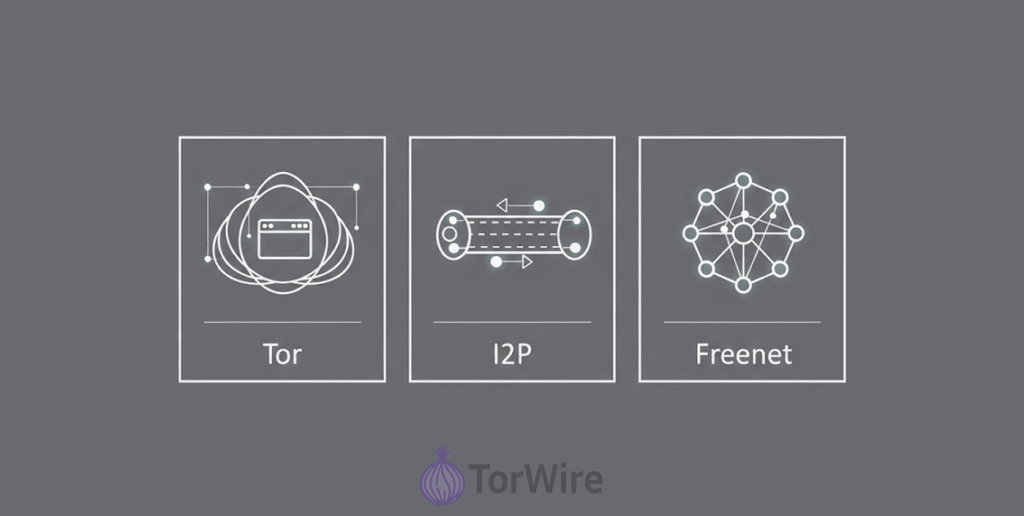
When most people think of the dark web (the actual name most often used), they think of Tor because of how big a part of the dark web this platform is. However, many people actually do not realize that Tor is one of many networks developed for many different purposes (being anonymous, privacy, to be uncensored, etc.)
As a result of this varying set of expectations and requirements from each individual’s dark web experiences, each type of dark web network will provide you with an optimal type of usage experience due to its own respective idiosyncratic features. Some of the types of networks that you may encounter on the dark web include Tor, I2P, Freenet, ZeroNet, and GNUnet.
All five of these networks are characterized by their distinct features related to anonymity and decentralization, as well as the ability to bypass governmental censorship; however, these distinctive features will be discussed separately for each network listed above.
1. Tor (The Onion Router)
Of all the online places to go (e.g., web servers, etc.), it is highly likely that if “the dark web” had a “capital city,” it would be “Tor.” Due to the popularity of the Tor Network and its high level of involvement by users, most people seem to use Tor when they are “going dark.”
How Does Tor Function?
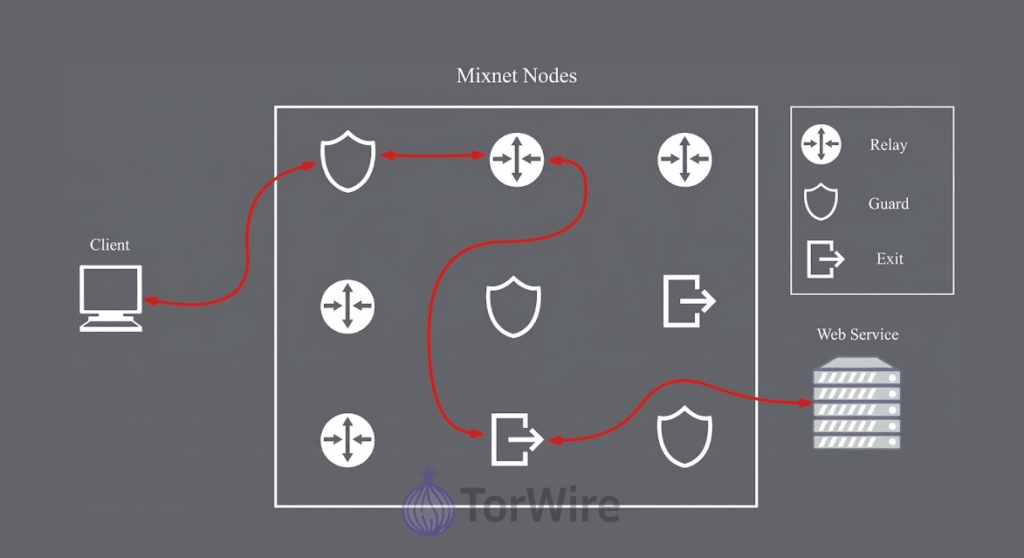
The routing method that Tor uses is referred to as ‘onion routing’. When you connect to a website over the Tor network, you are actually sending your information to a number of computers called relays that are run by volunteers rather than sending it directly from your computer to the web server”.
- Each relay only knows two pieces of information
- Where the data originated
- Where the data is intended to go
No single relay has any knowledge of the overall route. Hence, to protect the information being transmitted, several layers of encryption are applied to the information (this is akin to how an onion has multiple layers).
When the information is decrypted by one of the relays before being transmitted to the next relay, only the information necessary to transmit the data along to the next relay is revealed. Once your traffic leaves the Tor network, it is almost impossible for it to be tracked back to you. Because of this, Tor has a fantastic ability to provide private web surfing, bypass local censorship, and provide a means of communicating securely between users.
Common Sites on Tor
There are more than 10,000 hidden services hosted on the Tor network; many of which are through a special type of domain known as .onion.
Some examples of these services include:
- Anonymous marketplaces
- Political forums
- Whistleblower platforms
- Secure email providers
- Privacy-focused blogs
- Cryptocurrency services
- Secure chat systems
Some mainstream organizations even maintain Tor versions of their websites — including major news outlets and privacy advocacy groups.
Is Tor Safe?
It’s true that Tor gives you great anonymity, but does not guarantee that your anonymity is foolproof. The major weak point of the Tor network is the exit node; this is the last relay that passes your traffic from the Tor network onto the regular internet.
If your traffic is not encrypted (e.g., HTTPS is not used), the exit node will be able to see your data going through. For this reason, it is critically important that you follow the direction of the security experts:
- Use HTTPS everywhere
- Avoid logins to personal accounts
- Run Tor alongside a reliable VPN
- You can substantially increase your level of online protection by utilizing some form of secure (OpSec) operational security.
If used correctly, Tor is one of the strongest anonymity tools available to you.
How to Access Tor
Setting up Tor is very easy:
- Go to the Tor Project website to get a free download of the Tor Browser.
- Install and launch the browser.
- Connect to the Tor network.
- Visit .onion sites or just use the web anonymously.
Tor allows both novice and experienced users to browse the internet anonymously and has gained worldwide adoption.
2. I2P (Invisible Internet Project)
The Invisible Internet Project (I2P) provides a trusted anonymous network for internal communications and lets users access the public internet anonymously. Therefore, I2P is essentially a private anonymous network that resides on top of the internet.
How I2P Works?
I2P routes traffic entirely within its own network, rather than exiting frequently to the regular web. This allows it to optimize for:
- Secure messaging
- Anonymous file sharing
- Hidden website hosting
- Decentralized Forums
Garlic routing, which is bundled and used as an anonymous network that hides your traffic, is the method I2P has employed instead of Onion Routing as a means to obfuscate traffic patterns. In this way, garlic routed traffic is superior for peer-to-peer communication.
Common Services on I2P
- Secure messaging platforms
- Anonymous blogs
- Peer-to-peer filesharing service
- Decentralized forums
- Hidden marketplaces
Websites that use the I2P network are generally referred to as “eepsites” and have a website suffix of .i2p.
Is I2P Secure?
Yes, but I2P requires more technical knowledge than Tor.
Incorrectly configured I2P setups may leak your IP address and reduce your anonymity; however, if I2P is set up correctly, it will provide a high level of security, especially when users favor privacy on their internal network, rather than privacy on the public web.
How to Access I2P
- Download the I2P router software.
- Install and configure it.
- Set up your browser to route traffic through I2P’s local proxy.
- Access eepsites through your configured browser.
Due to the complexities involved in setting it up, I2P tends to attract a more technical type of user than Tor.
3. Freenet
Freenet operates on a fundamentally different philosophy, which above all prioritizes building a system that is able to resist censorship.
It achieves this by not routing data through a series of known relays (as Tor does), but rather by creating a distributed network for storing data and allowing users to share their unused hard drive space to store encrypted data.
How Freenet Works?
Data uploaded to freenet will be encrypted and broken into small pieces that will be distributed on many different locations (nodes). No single user knows what data they’re storing.
Freenet’s decentralized design makes it nearly impossible to control, remove, or censor information, as it lacks central servers.
Content Found on Freenet
- Political materials
- Activist publications
- Whistleblower documents
- Research archives
- Censorship-resistant blogs
Its design makes it especially popular in regions with strict internet censorship.
How Freenet Guarantees Anonymity
All data uploaded to freenet have been encrypted, broken up into fragments, and passed through many different nodes, ensuring that:
- Users do not know what they are hosting, and assist in providing anonymity to the uploader
- Observers can’t easily trace data origins
- Content removal becomes nearly impossible
How to access Freenet
- Download the Freenet client.
- Install and run the software.
- Use its built-in browser to explore Freenet content.
- Use trusted peer connections to provide greater anonymity.
4. ZeroNet
ZeroNet builds on Bitcoin, BitTorrent, and cryptography to securely distribute data over peer-to-peer networks, creating fully decentralized websites.
How ZeroNet Works?
ZeroNet hosts sites differently from centralized servers, with sites being:
- Identified by cryptographic keys
- Shared peer-to-peer
- Synced in real time
Users visiting a site automatically help host it, distributing the load across the network.
Key Features of ZeroNet
- No central servers
- Real-time site updates
- High resistance to censorship
- Decentralized authentication
- Fast loading for small websites
How to Access ZeroNet
- Download the ZeroNet client.
- Launch the application.
- Access ZeroNet sites via your regular browser using local addresses.
5. GNUnet
GNUnet stands out as the most technically advanced and complex dark web network. Instead of concentrating on one function, GNUnet allows users to build any type of secure and decentralised network they choose.
How GNUnet Works?
- Distributed hash tables (DHTs)
- Advanced encryption
- Peer-to-peer routing
- Anonymous communication protocols
Its architecture supports everything from:
- Secure messaging
- Anonymous browsing
- File sharing
- Decentralized services
Who Uses GNUnet?
The primary users of GNUnet include:
- Privacy researchers
- Cryptography experts
- Cybersecurity professionals
- Developers building secure communication systems
How to Access GNUnet
Accessing GNUnet usually involves:
- Command-line installation
- Manual configuration
- Advanced networking setup
Due to its complexity, GNUnet is primarily for technical experts.
Comparison of the Dark Web Networks
| Feature | Tor | I2P | Freenet | ZeroNet | GNUnet |
|---|---|---|---|---|---|
| Primary use | Anonymity, browsing .onion sites | Peer-to-peer communication | Censorship-resistant file sharing | Decentralized websites | Secure, decentralized networking |
| Access method | Tor Browser | I2P Router | Freenet Client | ZeroNet Client | GNUnet Software |
| Speed | Moderate | Faster for internal traffic | Slower due to data replication | Fast for small sites | Variable, depends on setup |
| Security level | High (with proper configuration) | High for internal communications | Strong for stored data | Moderate, focuses on decentralization | Very High, advanced encryption |
| Popular with | General public, journalists | Privacy advocates, tech-savvy users | Activists, researchers | Decentralization enthusiasts | Privacy researchers, developers |
What are the Risks of Dark Web Networks?

All networks found on the dark web have inherent risks, as all networks attract hackers, scammers/malware distributors, etc., and law enforcement will provide enforcement.
Let’s look at some of the major risks associated with each type of network within the dark web.
Tor Risks
- Exit node monitoring
- Malicious websites
- Phishing attacks
- Malware downloads
- Traffic correlation attacks
I2P Risks
- Misconfiguration exposure
- Smaller anonymity pool
- Traffic pattern analysis
Freenet Risks
- Hosting illegal content unknowingly
- Legal risks
- Complex security configuration
ZeroNet Risks
- IP exposure
- Malware propagation
- Limited encryption
GNUnet Risks
- Configuration complexity
- Experimental vulnerabilities
- Steep learning curve
Who Uses these Dark Net Networks and Why?
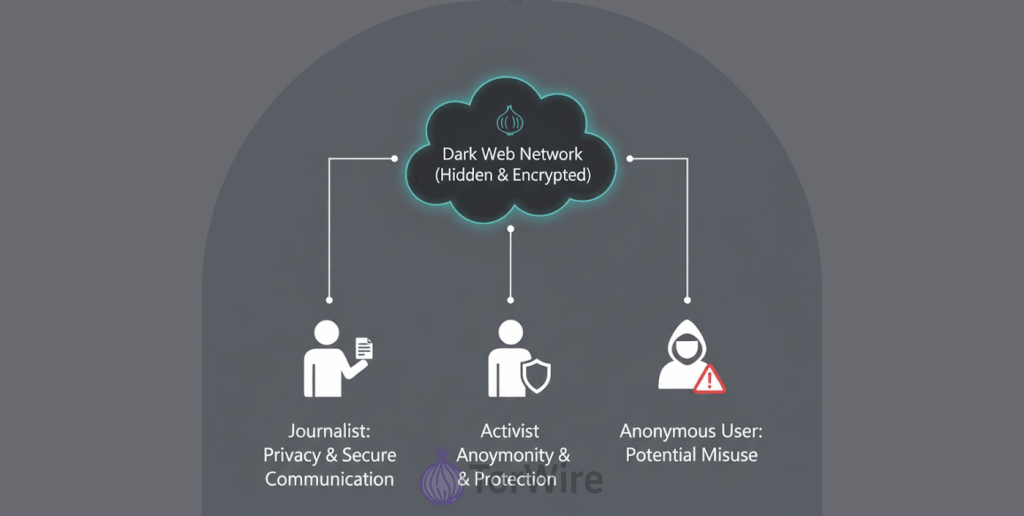
The dark web isn’t just for criminals, far from it. People use dark web networks for a wide range of legitimate, ethical, and even heroic purposes.
Common Reasons People Use the Dark Web
- Evading censorship
- Protecting identity
- Secure communication
- Whistleblowing
- Journalism
- Political activism
- Privacy protection
- Research
Who Uses Which Networks?
- Tor: Journalists, activists, general users, whistleblowers
- I2P: Privacy advocates, tech-savvy users
- Freenet: Activists, researchers
- ZeroNet: Developers, decentralization enthusiasts
- GNUnet: Cybersecurity experts, cryptography researchers
Is It Against the Law to Enter the Dark Web?
Many people do not know that accessing the Dark Web is not illegal in most nations. The use of Tor, I2P, and other Dark Web technologies is completely lawful. They are simply privacy technologies. However, what you do on the dark web can absolutely be illegal.
High-risk illegal activities include:
- Buying or selling drugs
- Purchasing stolen credit card data
- Hiring hackers
- Accessing illegal pornography
- Ordering forged documents
- Trading ransomware and malware kits
To put it another way, being anonymous does not mean that you are free from punishment. Law enforcement agencies around the world are keeping an eye on dark web criminal behavior and shutting down illegal marketplaces on a regular basis.
1. Marketplaces
Anonymous markets sell everything from books to highly illegal goods.
They often use:
- Cryptocurrency payments
- Escrow services
- Reputation systems
2. Hacking Forums and Cybercrime Services
These spaces offer:
- Malware development
- Ransomware-as-a-service
- Phishing kits
- Stolen credentials
3. Information Dumps and Leak Sites
Platforms where:
- Stolen databases
- Government leaks
- Companies publicly disclose breaches
4. Whistleblower Platforms
Reporters and whistleblowers often use these platforms to submit sensitive information safely.
5. Forums and Communities
Discussions on:
- Privacy
- Cryptography
- Politics
- Philosophy
- Security research
6. Search Engines and Directories
Since Google can’t index the dark web, users rely on:
- Hidden Wiki
- Ahmia
- NotEvil
7. Cryptocurrency Services and Mixers
Used to:
- Obscure transaction trails
- Improve payment anonymity
Safer Methods to Access Materials from the Dark Web

Whenever you engage in activities on or related to the dark web, your top priority should be safety.
Do
- Make use of an appropriate and effective VPN service
- Keep your OS updated
- Enable full-disk encryption
- Use strong passwords
- Enable two-factor authentication
- Isolate activities using virtual machines
Don’t
- Download random files
- Click unknown links
- Use personal emails
- Log into real accounts
- Share personal information
FAQs
Yes, it’s possible, but access depends on the dark web network. Tor supports Android officially, while iOS requires third-party apps. Other networks like I2P, Freenet, and GNUnet need technical setup, making them less mobile-friendly.
Anonymity refers to having no recognizable identifiers from public records. Pseudonymity involves the creation of a persistent alias (like a username or wallet address) that develops a reputation without linking to the actual individual.
Cryptocurrencies enable dark web payments without banks, but most are traceable. This has driven the use of privacy-focused coins and mixing services despite increased regulation and monitoring.