Your password or your company’s may already be up for sale on the dark web. The real question is: how would you know if it had happened?
Many data breaches go unnoticed for months. In fact, research shows companies take an average of 194 days to detect a breach, giving cybercriminals plenty of time to misuse stolen data. By the time a breach is public, the damage is usually done.
The financial impact is just as alarming. Businesses will spend an average of $4.88 million responding to data breaches in 2024, according to IBM’s Cost of a Data Breach Report. That’s why dark web monitoring is no longer optional. It’s a necessity for individuals and businesses in 2026.
Dark web monitoring works as an early warning system, continuously scanning hidden forums and marketplaces for exposed credentials or sensitive data. In this guide, we’ll break down how dark web monitoring works, what it can do for you, and whether it’s worth the investment.
What’s Dark Web Monitoring?

Dark web monitoring is a cybersecurity solution that examines the dark web to see if your private information is on it. The tools are kinda like special search engines, but not for indexing regular websites. They instead scan hidden forums, underground chat rooms, and encrypted marketplaces where criminals hide to trade stolen information.
Here’s one thing that makes dark web monitoring tools different from regular security tools like antivirus software. Antivirus blocks malware and firewalls prevent attacks, but in the case of monitoring tools, they tell you when your data has already been stolen. Though it detects after the breach, this detection is still very important because sometimes your security systems might fail, and the attacks succeed in leaking your data.
It works nonstop, tracking predetermined information like email address, company employee credentials, your bio data, customer information, proprietary business data, etc. When it finds something that matches your criteria on the dark web, it alerts you immediately.
Some sources of dark web monitoring tools include:
- Hidden markets where hackers sell stolen data
- Hacking forums where cybercriminals share information
- Encrypted messaging channels used by a cybercrime group
- Private chat rooms and darknet platforms
- Paste sites where threat actors post leaked data
According to research from Stanford, the majority of (88%) breaches in data occur due to human error. You can have all the fancy security in the world, firewall passwords, two-factor authentication, you name it, but all it takes is one person screwing up, clicking the wrong link, or using a weak ‘password123,’ for some hacker to get access to your private info.
Next thing you know, your data’s out on the dark web, probably being sold for the price of a burger. Without dark web monitoring on guard for leaks, you’d be clueless while things spiral out of control. By the time you notice, the damage is already done.
How Does Dark Web Monitoring Work?

Dark web monitoring protects your data through a number of technical steps that work in harmony, and when you understand the process, you’ll see why it’s effective.
Step 1: Automated Crawling
Specialized crawlers are always on the hunt across the dark web, slipping through the Tor network and other tools that hide their tracks. These aren’t your average Google bots. They access .onion sites, encrypted forums, and invite-only marketplaces that require the right credentials to enter.
You tell them what to look for, maybe it’s your company’s domain, the pattern of your employees’ emails, the structure of your customer databases, or just your brand name. They keep an eye out for those specific details.
Step 2: Data Matching and Validation
Once the system finds something, it checks if it matches your private data. Let’s say it spots ‘[email protected]’ dumped on some Russian hacking forum and flags it right away.
Smart systems use AI and machine learning to keep the noise down. They track real data leaks, not mere mentions of your company.
Step 3: Threat Intelligence Gathering
Great dark web monitoring doesn’t just stop at finding your data. It digs deeper, hunting for context like:
- Who’s actually selling or sharing it
- How much they’re charging, which tells you how valuable it is to criminals
- How fresh is the data: leaked yesterday or old news?
- What additional information comes bundled with it?
- Patterns suggesting a coordinated attack
Step 4: Real-Time Alerts
When the system detects a compromise, it sends you a detailed alert. The best services don’t just send raw alerts; they provide useful details, including what was exposed, where the data appeared, and the actions you should take next.
Step 5: Continuous Monitoring
This whole process never stops. Hackers don’t clock out at 5 p.m., so your monitoring can’t either. There’s always something out there: new leaks, fresh posts on forums, and listings on shady markets on the dark web.
Picture this real-life scenario, with the help of dark web monitoring, a medium-scale healthcare company discovers that someone is offering the login details of one of its employees for sale for $350. They quickly lock the account, update passwords, and investigate how the breach occurred.
This proactive step helps them save significant time and money that would have been spent on damage control if criminals had used the data for malicious purposes. If they weren’t on the lookout, they wouldn’t have found out until attackers used those credentials to carry out a ransomware attack months after.
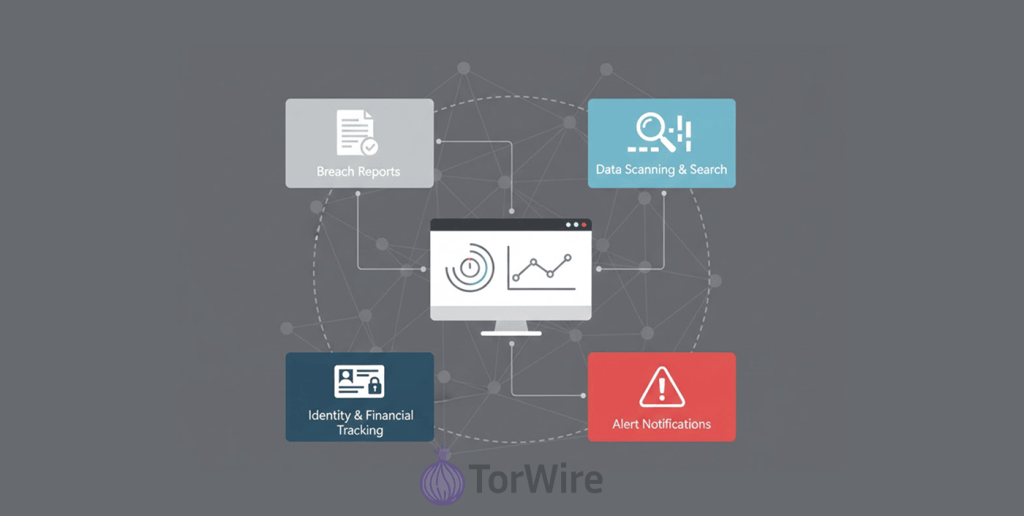
Features of Dark Web Monitoring

Effective dark web monitoring tools come with essential features that boost their performance. Here are some of the key features you should look for when choosing a good dark web monitoring tool:
- Threat intelligence really matters here: The monitoring solution doesn’t just spit out random alerts; it actually gives you a sense of who’s behind the threats and how they operate. You start seeing the bigger picture, not just raw alerts.
- Threat hunting takes things up a notch: The service works like you already have a target on your back, as if someone’s already trying to break in. It scans every nook and cranny for unusual activity, helping you catch issues early and prevent damage before it spirals out of control.
- Good monitoring tools are known for their quick incident response: Learning about a breach within hours instead of months lets you act quickly to stop threats before attackers can cause serious damage.
- Integration into existing security platforms: The whole thing ties into your other security tools, too. So all the data from your dark web monitoring flows into your main security system, giving you a clearer view and helping you spot patterns you might’ve missed otherwise.
- Stuck with generic settings: Most services let you customize what you want to watch, so you’re tracking the stuff that matters most to your business.
- Low false positives is another very important feature too: Most tools use AI and machine learning to filter out irrelevant matches, so you don’t get overwhelmed by useless alerts.
- Historical data: Access to compromises that happened in the past can help you when connecting the dots and recognizing patterns, so you can know which threat is new and which ones are recurring.
Why Use Dark Web Monitoring?

The problem doesn’t end with compromised credentials; an even greater threat arises once the data reaches the dark web. With a dark web monitoring tool, you can intercept account takeovers, financial frauds, and even targeted scams before they happen. How? Because all these start with just a simple leak of your password, personal info, or bank details.
And data breaches are more common today than they used to, so it’s no longer a matter of ‘if’ they’ll happen but ‘when’ they’ll happen. Smart businesses use dark web monitoring not because others are using it, but because it’s essential for several strategic reasons:
The dark web is like an early warning system for your business. Sometimes, you’ll hear the chatter before an attack even starts. Other times, you spot trouble with your supply chain partners, and that’s a big deal, because their problems can quickly become your problems, even if your own defenses look solid.
Dark web monitoring for businesses provides 24/7 surveillance of potential threats, keeping you protected even outside normal business hours when most attacks occur.
As you monitor the dark web, you will be able to piece information together. When your company name or data appears on a shady forum, you can start connecting the dots to identify who might be targeting you and what they want with the information.
In monitoring, you will also begin noticing various risk types, including third-party breaches, data dumps on hacker sites, leaks from P2P networks, accidental exposures, brand impersonation, domain spoofing, and other budding threats even before they materialize.
Think of dark web monitoring like sending a canary into the coal mine – it warns you in advance in the event you need to react proactively to an impending threat.
Is Dark Web Monitoring Legitimate?

You may be wondering: Is dark web monitoring even a legal practice? I mean, monitoring tools infiltrate private chat rooms and some invite-only forums to collect information, so worrying about its legitimacy is totally normal. But yes, it’s a legal security practice; however, there’s a limit to what it can and cannot do, and it’s important you take note of these.
The tools themselves don’t do anything illegal; they’re just equipped with some special software that searches the dark web to keep track of when your information may show up there. They work similar to how Google crawls the regular web, only this time it’s poking around in the darker corners.
If your data winds up on the dark web, these tools can’t make it disappear. There’s no help desk or friendly support agent down there who’ll delete your info because you asked nicely. The dark web’s anonymous, locked down tight, and pretty much a free-for-all.
What these monitoring tools can actually do is give you a heads-up. Your information pops up somewhere it shouldn’t? You’ll receive an alert, giving you a chance to protect yourself, change your passwords, enable multi-factor authentication, notify anyone affected, and strengthen your security before attackers cause real damage.
Dark web monitoring won’t stop bad actors from using your stolen data. If someone already has your credit card number or login, the tool can’t block them from trying it out. What it gives you is speed, an early warning so you can jump in and limit the fallout.
And honestly, if you ask me, that’s the real value. When a data breach occurs, you can detect it sooner, usually within hours instead of after months of ignorance. This means less of a time frame for criminals to exploit your personal information for nefarious purposes.
Benefits of Dark Web Monitoring

Dark web monitoring isn’t just about catching stolen passwords. There’s a whole lot more you get out of it:
1. Spotting Breaches Faster
Traditional security tools take their sweet time, about 194 days on average, to notice a breach. That’s more than six months where criminals could be poking around your data. With dark web monitoring, you’re talking hours or days, not months.
The minute your data shows up on shady forums, you get the heads-up. That’s huge. Every extra day crooks have your info, they can steal money, mess with your systems, or sell your details to anyone who’ll pay. Cut that time down, and you’re saving yourself a fortune and a lot of headaches.
2. Protecting Your Finances
Data breaches aren’t just embarrassing; they are extremely costly. As per IBM’s 2024 research, the average cost of a data breach equals $4.88 million. That’s fines, legal bills, lost customers, and all kinds of fallout. Dark web monitoring helps you spot breaches early so you can:
- Change hacked passwords before the bad guys do real damage
- Warn your customers before anyone tries to use their data
- Dodge fines for dragging your feet on disclosure
- Proof that you’re serious about keeping your customers’ data safe
3. Competitive Intelligence
Sometimes threat actors discuss next steps, which company they’re targeting, and how they intend to go about it. Dark web monitoring alerts you to attacks on companies like yours and notifies you if a competitor is hacked.
This kind of info is gold, lets you spot new threats early and see what hacking tricks are making rounds, so you fortify your defenses before they hit you. When you know what’s out there, you’re a step ahead, ready to deal with those attacks if they come your way.
4. Keeping Regulators Happy
Regulations such as GDPR, CCPA, HIPAA, and PCI DSS aren’t mere suggestions; they’re mandatory. They require you to protect personal data and report breaches fast. Dark web monitoring makes it way easier to:
- Detect and report breaches quickly (and avoid big fines)
- Show you’re doing your homework on security
- Keep a record of your security efforts
And those fines? GDPR fine alone can hit you for up to €20 million or 4% of your global revenue. Small data breaches can become costly if left undetected.
5. Protecting Your Reputation
To earn your customers’ trust isn’t a walk in the park; it takes years, and losing it is a price you don’t want to pay. Imagine your customers finding out their data was leaked while you stayed unaware for months and didn’t report it. They’ll lose trust in you. With dark web monitoring, you’re always in the know.
If you spot issues early, you can actually let people know t what’s happening and what you’re doing about it, no need to cover it up. People respect the openness and want to know they can rely on you to handle things when it gets messy. That’s how you keep customers safe. In return, they give you their trust, and your reputation stays intact, too.
6. Watching Your Supply Chain
You don’t work alone. If a partner, vendor, or service provider gets breached, you might be next in line. Dark web monitoring can tip you off when someone in your supply chain is compromised. Say your payment processor’s credentials pop up on the dark web — you can lock things down before anyone tries to use them against you.
Who Actually Needs Dark Web Monitoring?
Honestly? Pretty much everyone. If your business handles sensitive data, such as credit cards, health records, social security numbers, anything like that, you’re a target. Got intellectual property or trade secrets? Those fetch a high price on the dark web, too.
Organizations in finance, healthcare, government, or critical infrastructure are obvious targets for hackers and nation-state actors. But small and midsize companies shouldn’t get complacent. Hackers love going after smaller businesses because they know your security isn’t as strong, but your data is just as valuable.
So, is dark web monitoring worth it? Absolutely. It sheds light on threats regular security tools might miss. Serious about beefing up your security? Now’s the time to make dark web monitoring part of your defense plan.
How Does Personal Information Get on the Dark Web?
Ever found your information on the dark web? It can feel scary, no doubt, but knowing’s always better than not knowing because when you are aware, you can actually do something about it. Here’s how your data gets there in the first place:
1. Phishing Attacks: The Classic Trick
Phishing is still the number one way criminals steal information. They send emails that look completely legit, maybe from your bank, a shipping company, or even your own IT team, hoping you’ll click a link and hand over your login details.
These scams are getting tougher to spot. Just one person clicking a fake “reset your password” link can give hackers access to an entire company’s network.
2. Malware and Credential Stealers
Hackers aren’t always using obvious viruses anymore. In fact, CrowdStrike found that79% of attacks didn’t even use traditional malware, instead they log in using stolen usernames and passwords or built-in system tools that slip past the notice of your antivirus.
When they do use malware, it’s usually those very sneaky infostealers like RedLine, Raccoon, or Vidar that quietly steal passwords saved in your browser and send them to the criminals.
3. Data Breaches at Third-Party Companies
Sometimes you do everything right when it comes to security, yet your information might still appear on the dark web. Your data often comes from the companies you deal with; when they’re breached, your information is affected too.
Take, for example, Equifax’s 2017 data breach. It exposed personal info for, get this, 147 million peeps. And then, just a couple of years later, in 2019, Capital One got hit with a hack that messed up about 100 million customer accounts, and then in 2021, T-Mobile’s data breach compromised the personal info of 50 million people. Each of these dumps ended up for sale on the dark web.
4. Database Screw-Ups and Leaks
Sometimes it doesn’t even take a hacker. Companies accidentally leave databases or cloud storage wide open, leaking information for anyone to find. In 2019, someone found 419 million Facebook records just sitting on an exposed server.
Criminals are always on the lookout for slip-ups. If they spot one, they’ll jump at the chance, either to sell your info on the dark web or just steal your money themselves.
5. Attacks on Unsecure Networks
Ever used public Wi-Fi? You’re sitting in a coffee shop or waiting at the airport, and when you connect to free Wi-Fi, you’re easily at risk of ‘man-in-the-middle’ attacks because security on public Wi-Fi is porous.
If you fly naked on public networks, attackers nearby can intercept everything you send, whether it’s passwords, session cookies, or your private information. Some cybercriminals even set up fake WiFi hotspots with names like ‘Free Airport WiFi’ just to steal your data.
6. Ransomware Attacks With Data Theft
Today’s ransomware has gotten way better; they don’t just encrypt your files anymore, attackers go further to steal sensitive data before locking up your systems.
Even if you restore your backups, they threaten to leak the data unless you pay up. Groups like Conti, LockBit, and BlackCat post stolen info on dark web “leak sites,” pressuring victims and showing off for future targets.
7. Packaging and Selling Stolen Data
After stealing all this info, criminals organize it into “fullz,” complete identity profiles with your name, birthday, Social Security number, address, financial details, and more, and can sell it as cheaply as $30 on various dark web markets, depending on how valuable they think the victim is. For a deeper look at where these transactions actually take place, see our guide to the top dark web markets.
Some hackers’ specialty is to collect data and repackage it, and then resell it to other criminals who do the actual fraud.
What It Means If Your Data Shows Up on the Dark Web

If you find your data on the dark web, it’s not the time to start panicking, nor should you sit and do nothing. Change all your passwords right away. Watch your credit reports like a hawk, and if you can, swap out your credit cards. Keep an eye out for anything weird on your accounts.
To be honest, there have been many major cybersecurity incidents over the last few years. We have seen breaches with more than 100 million records exposed. Your information has likely already been sold on this or another market. If you had no idea this happened, you are not alone.
The cost of failure for businesses is huge as well; as businesses, they are now responsible for protecting customer information, and failing to protect customer information creates liabilities.
The damage from a breach can lead to a total loss in reputation overnight. When customers no longer trust the business, there is negative publicity, and as a result, there are lawsuits or government investigations for the company as well.
Breaches carry huge financial costs, from regulatory fines and legal fees to business interruptions and customer notifications, which can escalate quickly.
And the danger doesn’t end with the first breach; criminals often reuse stolen data in other attacks, like credential stuffing. Once it gets out that your defense was once compromised, you’d remain on their radar for a long time.
This means your personal information, money, and identity may be compromised and could be in danger at this very moment. More often than not, this would be related to your personal or financial account credentials being stolen, or personal information that could be used to steal your identity or access your accounts.
Don’t waste time, secure your accounts and personal information ASAP so that whatever is out there becomes useless to criminals, and they can’t steal your identity or your money.
Is Dark Web Monitoring Worth It

Whether it’s worth sparing a budget on dark web monitoring actually depends on your specific situation. Like who you are, what kind of business you run, and what exactly you’re protecting and how valuable it is.
Let’s start with big companies:
If you’ve got millions of customer records, there’s no question—get dark web monitoring. Yes, it costs anywhere from $10,000 to $100,000 a year, but that’s pocket change compared to the average cost of a data breach, which hits nearly $5 million.
Prevent just one major incident, and the service pays for itself for years. Plus, regulations like GDPR, CCPA, and HIPAA pretty much require you to have this kind of protection.
Small and medium businesses? You shouldn’t skip it either. You might not have a huge security team, but you’re still a target, maybe even more so, since hackers know your defenses are weaker. Dark web monitoring helps level the playing field.
For $100-$1,000/month, you can detect threats that might otherwise go unnoticed. There are estimates that 60% of small businesses fail within six months following a significant breach; this statistic is difficult to overlook.
Business owners, senior managers, and others with positions of responsibility or high net worth possess the most to lose; thus, if your identity were stolen or if you suffered a financial loss, you will want to monitor your accounts for approximately $15-$30/month.
This is a small investment in order to maintain peace of mind and hopefully detect trouble earlier than you would if you did not monitor your accounts.
For everyone else, check what you already get for free. Lots of banks, credit cards, and identity theft services now include basic dark web scanning. See if you’re already covered through your bank, a credit monitoring service, or even your job’s benefits package; you probably don’t need to double up. But if you don’t, and you handle your own financial info, basic monitoring adds a helpful layer.
Don’t make the mistake of thinking dark web tracking is some kind of miracle cure-all. It has its limitations:
- It only alerts you after your data’s been stolen, not before.
- Once your information has been released into the public domain, it cannot be reversed; you can only react and try to prevent further damage.
- Not every corporation that is hacked has its information sold publicly; instead, the hackers keep their information to themselves or sell it directly to buyers.
- And if you ignore alerts, monitoring does nothing; you’ll need a plan already in place and be able to implement it quickly.
The bottom line? Dark web monitoring is only one piece of the puzzle in your entire security process. You also need the following measures in place to ensure robust security:
- Strong, unique passwords
- Multi-factor authentication
- Employee training
- Keep your systems up-to-date by regularly running security updates
- Endpoint protection, like running antivirus software
- Network security (having a reliable firewall)
- Have backups off-site
- And finally, having an incident response plan in place
You should use dark web monitoring as an early warning system. It lets you know when your other defenses have slipped. For most businesses handling sensitive data, it’s not just a smart idea, it’s a real investment in your future. To make truly informed investments, understanding the direction of cyber threats is crucial.
We analyze the major shifts to watch in our guide to cybersecurity trends and predictions. If you care about security, take a hard look at it. Most of the time, it’s worth every penny.
What to Do If Your Data Shows Up on the Dark Web
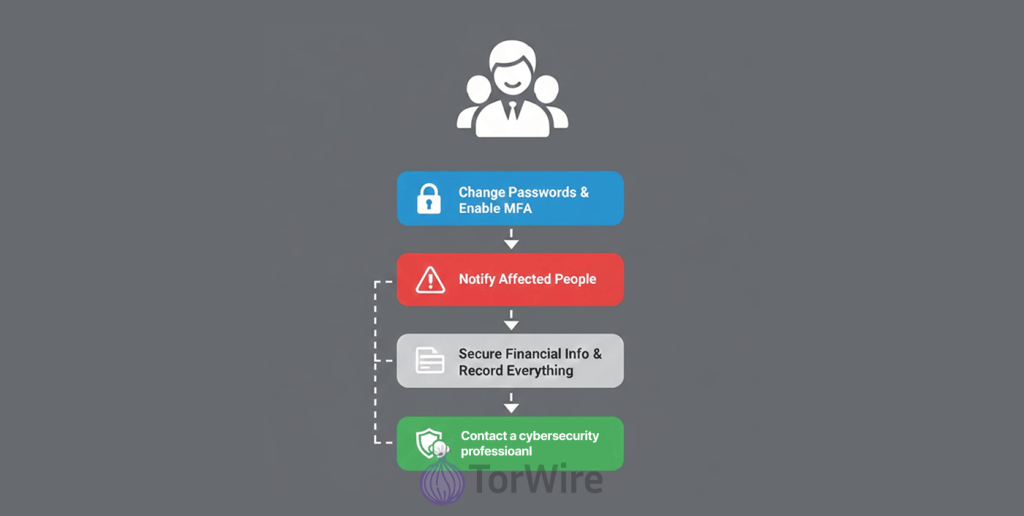
If you discover your data is circulating in the dark, we act fast:
- Change every password that was compromised, turn on multi-factor authentication on every account you can, and notify anyone affected, both customers, employees, and partners, of what happened.
- Keep an eye on your accounts for anything odd, and if you think your credit cards or other financial info leaked, just go ahead and cancel them.
- Your first call should be to a cybersecurity pro. They’ll walk you through exactly what to do next. And one very crucial tip: write everything down – every step, every click, every time stamp–document them all. If you ever need to prove what happened, either to your boss, bank, or even the cops, that record will be your best friend.
- Delay is dangerous. Acting fast will reduce the time attackers have to cause damage, giving you less to deal with later on.
Types of Dark Web Monitoring Tools
If you want to keep an eye out for when your info will appear on the dark web, there’s a bunch of options available for you, some simple, some all-in. Here are the tools on the market and how to figure out which one fits your needs:
1. Enterprise Dark Web Monitoring Platforms
ZeroFox, Digital Shadows (now known as Searchlight), and Flashpoint offer comprehensive monitoring services that cover every aspect of the dark web, including forums, black markets, messaging apps, paste sites, etc.
In addition, these service providers integrate seamlessly with your security stack (e.g., SIEM, orchestration tools), allowing you to create custom alerts for anything that is important to you.
Expect detailed threat intel reports and access to actual analysts when you need help. However, these tools are expensive, and their annual subscriptions can cost you anywhere from $10,000 to as high as six figures. They’re the way to go for large companies that have dedicated security teams and way more data to protect.
2. Identity-Focused Monitoring Services
If you’re concerned about your private data being compromised, consider monitoring services like Experian IdentityWorks, Norton LifeLock, or Aura.
These companies offer a service that will monitor your identity, alert you to known breaches, and provide add-on services such as identity theft insurance and recovery services.
The price tag for these monitoring services is between $10-$30/month, which makes them affordable for individuals, as well as, small business owners concerned with the ongoing threat of identity theft.
3. Credential Monitoring Tools
Consumers often just want to check if their username or password has been exposed. Have I Been Pwned, SpyCloud, and Password Alert can help.
The best part? Have I Been Pwned is completely free! The site will check against the world’s largest database of compromised accounts (over 12 billion and counting) for matches to the email address that was entered on the site.
Simply type in your email address, and you will find out how many times your email address was found in a breach. This tool is easy to use and is very effective, as most attacks will use stolen credentials!
4. Threat Intelligence Feeds
Services such as Recorded Future, ThreatConnect, and Intel471 provide real-time and raw data regarding any threats from various sources on the dark web. Security teams can integrate these into their existing systems for a broader picture. These are best if you actually have analysts who know how to use the info and respond.
Tips for Staying Accessing the Dark Web Safely

To start with, assess whether you really need to access it or not. While journalists, researchers, or people in heavily restricted countries can benefit from the dark web, most others should probably avoid it altogether.
Accessing the dark web carries significant risk and should not be done without serious precautions. For a complete breakdown of the tools, steps, and critical warnings, please read our dedicated guide on how to access the dark web safely.
If you do have a justified reason for accessing the dark web, here are ways in which you can try to protect yourself while doing so:
- Never share anything personal: Make up brand-new usernames and email addresses you’ve never used before. Don’t let anything connect back to your real life. If you are purchasing a product, use only prepaid, anonymous payment methods.
- Trust your guts: If you feel unsafe while using the dark web (like a website or a seller giving off a suspicious feeling), leave immediately. And don’t even think of opening just any link you see or opening random files, and never trust anyone who is promising deals that seem too good to be true. Things and people on the dark web aren’t always truly what or who they claim to be.
- Set up monitoring for identity theft: Some services will scan the dark web for your info and alert you if anything pops up. That early warning can save you a lot of trouble.
- Turn off Java and ActiveX: Hackers love these for sneaking into your system. Just disable them before you do anything else.
- Avoid downloading files from the dark web: As they often contain malware or viruses. If downloading is absolutely necessary, scan the file with up-to-date antivirus software before opening it.
- Make a separate non-admin account for browsing: Admin accounts make it way too easy for malware to take over your computer if you slip up. Stick to an account with limited permissions.
- Use VPNs: We recommend using a paid VPN like NordVPN for using the dark web due to the added layer of security against hacking through encryption of your connection, in addition to using Tor alone.
- Always update your antivirus regularly: Protect yourself from malware that exists on the dark web with an antivirus program such as TotalAV or Bitdefender.
Keep in mind that while many places allow for legal access to the Dark Web, if you break the law by purchasing illicit materials or engaging in criminal acts, you will be investigated and may face serious criminal repercussions. Law enforcement monitors the Dark Web.
Other Ways to Protect Yourself from Dark Web Threats

You can’t be completely safe from cyber threats by just implementing dark web monitoring alone; having other security measures in place is important:
- The biggest security risk doesn’t often come from your software; it’s often from your staff, that’s the weaklinks. Forget about the boring compliance videos; to build a strong cybersecurity culture, get hands-on. Run engaging training that teaches people to spot phishing emails (check that sender address!) and resist phone-based social engineering tricks. Then, test that knowledge under pressure. Run tabletop drills. Set up red team vs. blue team battles. This will show you where your actual weaknesses are, allowing you patch the cracks before a real attacker takes advantage of them.
- Your security is only as strong as your weakest link, which means protecting endpoints, cloud systems, identities, and sensitive information. Look for protective software that can identify and block threats automatically, actively hunt for issues, and give you instructions on what you should be prioritizing in the right order.
- Practice good IT hygiene, including performing a total inventory of every asset you own, both hardware and software, and continuous vulnerability management. You can’t protect what you don’t even know exists. You should know that consistent, thorough inventory and vulnerability management matter.
- Identity management tools are big here, too. Control every user account, set clear access rights, automate policy enforcement, and yank permissions fast when something looks off.
- And yes, keep those dark web monitoring tools running in the background. If they spot your data on a criminal forum, you get an alert right away and can jump on it.
Best bet? Don’t rely on just one thing. Stacking your defenses monitoring works best as part of a bigger security game plan, not as your only move.
FAQs
Exposed data such as emails, passwords, phone numbers, credit cards, IDs, etc. They look for information that attackers have already stolen and published publicly.
Very rarely. Dark websites use design and hosting methods that make takedowns difficult. The value for you is in the alert informing you of the exposed data, to enable you to safeguard your accounts quickly.
Credit monitoring will alert you to potential fraud after it has occurred (such as an application for a new loan). Dark web monitoring provides you with an alert as soon as your data is available on a hacker’s forum. This is the much earlier stage of fraud.
No. A good monitoring service will perform its job discreetly (quietly, without letting anyone know that someone is watching).
Some tools work well for basic scans to check whether your data has ever been compromised, such as Have I Been Pwned. However, if you need continuous and comprehensive monitoring beyond email addresses, paid services offer far better protection than free ones. You get what you pay for in speed and coverage.