-
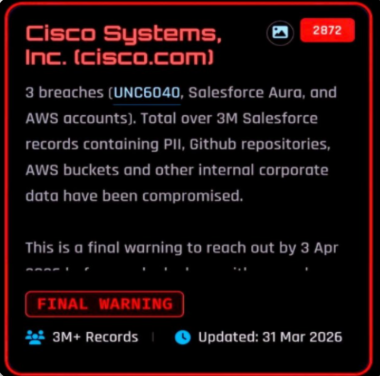
The hacker group ShinyHunters claims to have stolen over 3 million Cisco records from Salesforce and AWS.
-
They set a hard deadline of April 3 for Cisco to respond otherwise they’ll leak the data publicly.
-
The group shared screenshots showing access to Cisco’s cloud environment, hinting at deep infiltration.
The notorious hacking group ShinyHunters posted a final warning to Cisco on their dark web leak site. They’re giving Cisco until April 3 to make contact. If Cisco ignores them, the hackers promise to release stolen data and cause unspecified “digital problems.”
This threat comes just days after the same group leaked 350GB of sensitive European Commission data. That dump included mail server records, database exports, internal documents, and contracts.
Cisco Data Allegedly Accessed from Three Breach Paths
The hackers claim they got in using three separate routes. They named these paths as UNC6040, compromised AWSaccounts, and Salesforce Aura. All together, they say they grabbed more than 3 million Salesforce records.
The haul includes personally identifiable information, AWS storage buckets, GitHub repositories, and other internal corporate data.
The UNC6040 reference is a big deal. Google’s Threat Intelligence Group gave ShinyHunters that name in August last year. Even more interesting? Cisco itself had previously published details about a voice phishing campaign, called vishing that targeted its own employees.
By using that specific UNC6040 label, ShinyHunters isn’t just claiming a hack. They are suggesting that at least part of this data came from clever social engineering calls, not just technical exploits.
ShinyHunters Shares Proof of the Cisco Breach Online
To back up their story, the group shared three images. These screenshots don’t contain any customer secrets. But they do appear to show a dashboard of Cisco’s AWS environment.
You can see storage volumes and bucket listings. Seeing an organization-level view is a red flag. It usually means the hacker has control over multiple linked accounts and services under one central control, not just one small corner.
Although these screenshots don’t contain any sensitive information, they suggest the hackers accessed an entire cloud infrastructure, not just one isolated system.
A History of Salesforce Threats
ShinyHunters has pulled this move before. Over the past year, the hackers have come out to claim access to lots of Salesforce-related data across many big companies.
They often mention simple mistakes, things like misconfigurations, compromised credentials, or weak third-party integrations– as what allowed them entry. They rarely blame a flaw inside Salesforce itself.
Their pattern is predictable. First, they list the data on leak sites with vague details. If the company stays quiet, they publish full dumps. Some of the previous breaches had customer information, internal communications, and operational data from connected systems exposed to the public.
A lot of big companies, including Odido, Telus Digital, Farmers Insurance and SoundCloud, were the victims. Other victims include Crunchbase, GAP, Qantas, Vietnam Airlines, Alexander McQueen and luxury fashion wear manufacturers Gucci and Panera Bread. That is a long and worrying list.
Currently, no one has confirmed if these claims are authentic, and no word from Cisco yet concerning the matter. However, for now, everyone is watching how Cisco will handle this threat.
