-
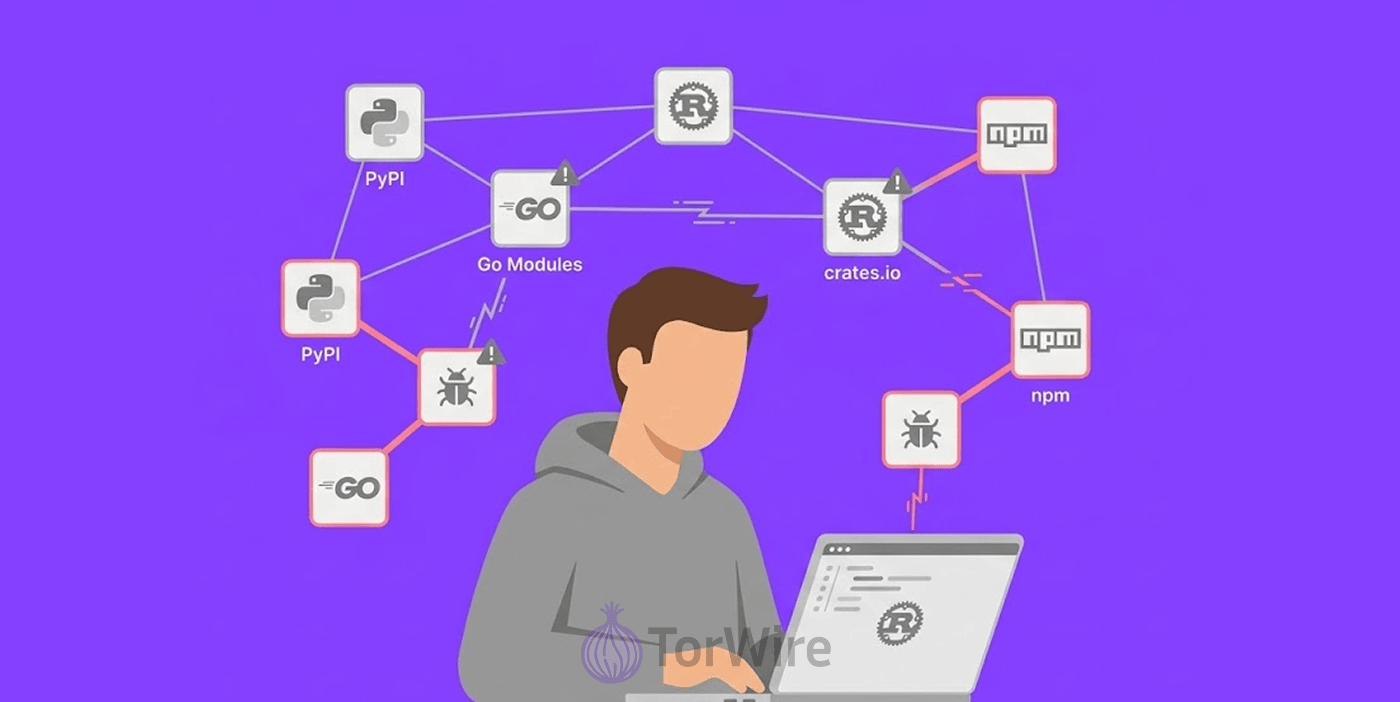
North Korean bad actors plant more than 1,700 vicious packages all over five open-source ecosystems such as Packagist, Rust, npm, Go, and PyPI, targeting developers across the world.
-
The packages mask themselves like legit developer tools but behind the scene, they act as malware loaders, stealing browser data, crypto wallets, as well as passwords.
-
The same bad actors have a parallel social engineering campaign ongoing with multi-week operations on Slack, LinkedIn, and Telegram, delivering fake meeting links that set up malware on Linux, macOS, and Windows.
Bad actors from North Korea just made their most ambitious move in software supply chain attacks, pushing vicious packages into prominent open-source ecosystems to target developers in any part of the world. This is the same bad hackers behind the persistent “Contagious Interview” campaign.
Hackers Conceal Malware Inside Dev Tools
In a report on Tuesday, Kirill Boychenko, the Socket security researcher flagged the malicious operation and warned that the hackers packages were designed to pass “the trusted developer tools test” while secretly running as malware loaders. Since January 2025, Socket has finished out over 1,700 malicious packages connected to the cross-ecosystem supply chain strike.
On npm, the group launched logger-base, dev-log-core, pino-debugger, logkitx, debug-glitz, and debug-fmt. On PyPI, they dropped apachelicense, logutilkit, license-utils-kit, and fluxhttp. What’s more! They pushed packages into Rust, Go, as well as Packagist under similarly convincing names.
What makes this campaign particularly nefarious is how the bad actors activate the malicious code. The malware does not trigger during installation. Instead, they hide inside seemingly legitimate functions that correspond with the advertised purpose of the package.
For instance, in the Rust package “logtrace,” the malware hides inside a method called “Logger::trace(i32)”. As soon as a developer runs the infested code, the loader retrieves a second-phase payload customized to the operating system of the victim.
That payload houses infostealer and remote access trojan (RAT) capabilities that targets password managers, web browsers, as well as cryptocurrency wallets.
The Windows version ushered in via “license-utils-kit” goes even further. Socket highlights it as a “full post-compromise implant”; one that deploys logs keystrokes, shell commands, uploads files, hijacks browser data, creates encrypted archives, launches AnyDesk for remote access, crashes additional modules, and generates encrypted archives.
Boychenko noted that this function makes the cluster “stand out not only for the extent it reaches across ecosystems, but for the depth of post-compromise attributes embedded into at least part of the campaign.”
This level of stealth and persistence mirrors the Notepad++ infrastructure hijack, where attackers maintained control over the software’s update system for six months, silently distributing malware to unsuspecting users before the compromise was discovered.
UNC1069 Runs Week-Long Social Engineering Operations
In addition to the North Korean hacking spree, a group influenced by money, UNC1069, (which overlaps with Sapphire Sleet, BlueNoroff, and Stardust Chollima) keep deploying a parallel campaign that targets individuals directly.
This group poisoned the popular Axios npm package to circulate an implant called WAVESHAPER.V2, taking over the npm account of the package maintainer through a tailored social engineering attack.
Security Alliance (SEAL) reported that between February 6 and April 7, 2026, it blocked 164 UNC1069-linked domains impersonating platforms like Microsoft Teams and Zoom.
UNC1069 operators run “weekly, low-pressure social engineering attacks on LinkedIn, Telegram, and Slack. They either pose as known contacts or trusted brands, or hijack access to already-compromised accounts before dishing out a fake Microsoft Teams or Zoom meeting link,” SEAL stated.
Those fake links serve ClickFix-style lures that execute malware connecting back to an attacker-controlled server. The malware then steals data and conducts targeted post-exploitation activity across Windows, macOS, and Linux.
SEAL also highlighted the group’s deliberate patience after gaining access. “Operators halt and do not take immediate actions after initial compromise. The implant stays idle for a while after the breach.
The target typically changes the schedule for the failed call and keeps running normally, without knowing their system is at risk. That patience elongates the attack window and harvests maximum value ahead of any incident response,” SEAL explained.
Microsoft Warns of Ongoing Evolution in DPRK Tactics
Microsoft is watching the same pattern unfold. The company confirmed that financially driven North Korean threat actors are actively shifting their tools and infrastructure, building domains that impersonate U.S. financial institutions and video conferencing apps.
Sherrod DeGrippo, Microsoft’s general manager for threat intelligence, put it plainly: “What we see often is steady growth in how these actors, linked to DPRK and have love for money, operate (new tools, new systems, new targets) but the act and intent remains just the same.”
Malicious packages no longer announce themselves. They wait, blend in, and strike only when no one is looking.