-
A new infostealer called Arkanix appeared on dark web forums at the end of last year and disappeared just two months later.
-
Security researchers found strong evidence that the malware was developed using AI assistance, drastically cutting development time.
-
The creator specifically designed Arkanix to exploit vulnerabilities in browsers, cryptocurrency wallets, VPN services, gaming platforms, etc. It allowed buyers to choose between modular and premium features.
A new malware also appeared then all but evaporated from dark networks overnight. The creator pulled the plug just two months after rolling it out.
Upon evaluation, security researchers at Kaspersky found something really interesting. Some parts of the code suggest the malware was written with the help of artificial intelligence.
Arkanix Stealer’s Code Suggests AI Helped Write It
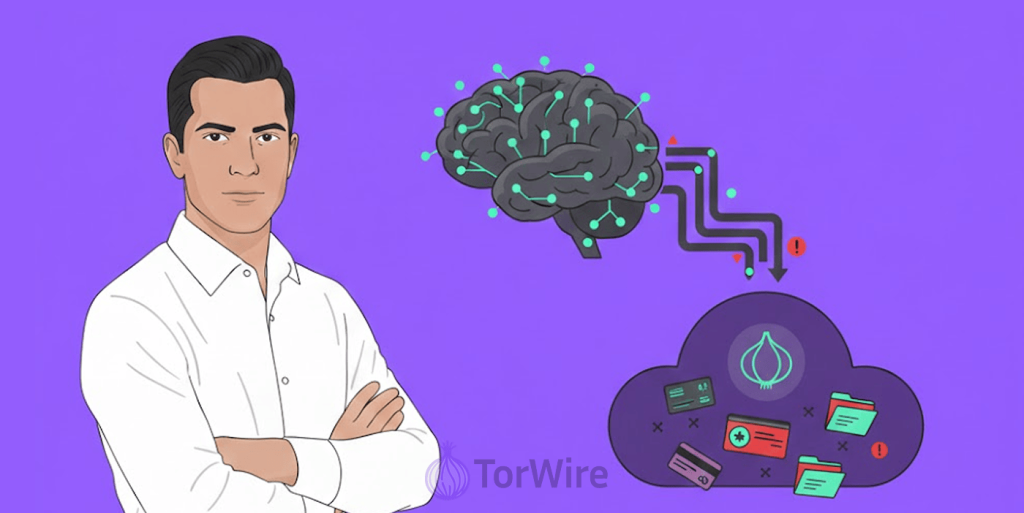
The first appeared last October on a hacker forum, offering two versions to potential buyers: the basic tier came written in Python, and the premium version used C++ with VMProtect for better stealth.
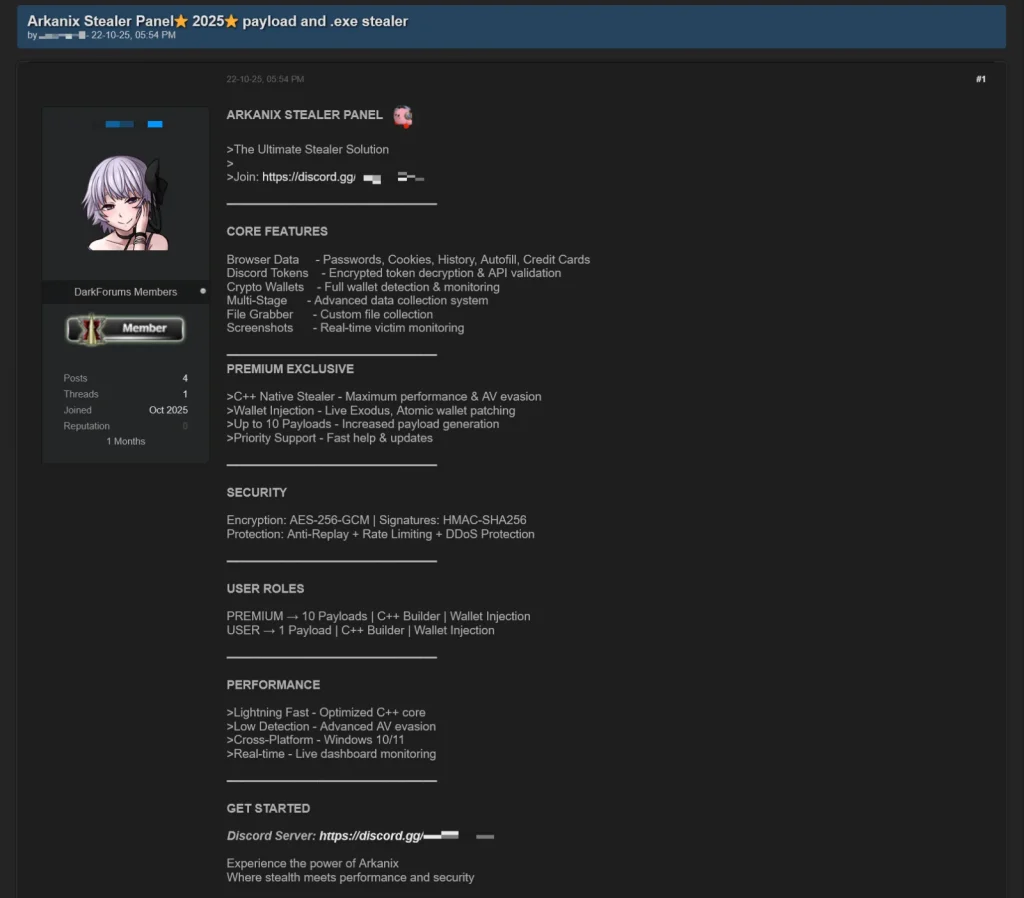
Arkanix Advertised on Hacker Forums
Source by: Kaspersky
Additionally, the creator of the malware actively engaged their user community through a Discord server platform to foster creativity, build feature enhancement requests, share experiences, and update themselves on any new developments. There was even a referral program where users got an extra free hour of premium access for bringing in new buyers. New customers also got a free week of the good stuff.
Then, in December last year, everything went offline, both the control panel and the Discord server; it all just vanished. Kaspersky researchers who looked into it believe the entire thing might have been an experiment. Like someone was testing how fast they could build working malware using AI.
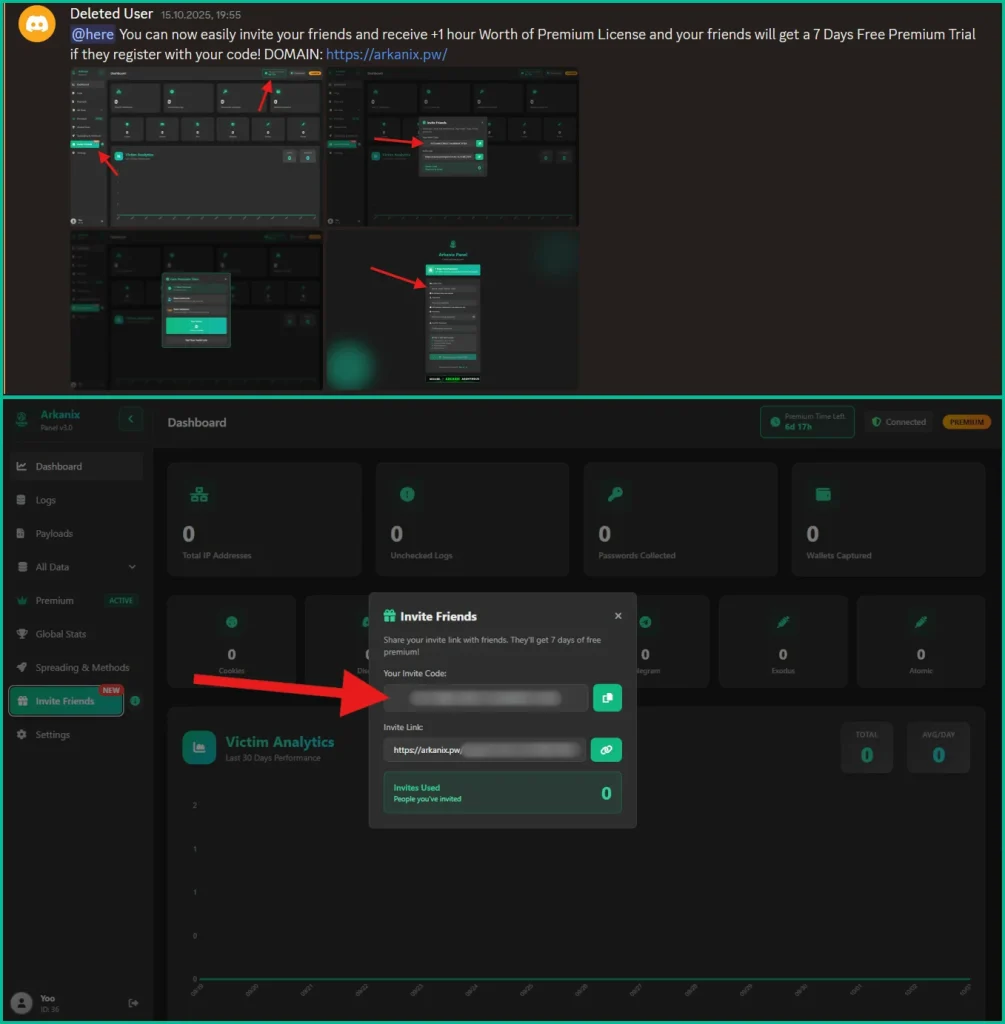
Dashboard-Based Referral Options
Source by: Kaspersky
The Malware’s Capability
Even though it didn’t stick around long, Arkanix packed serious heat. The basic version could steal system info, browser data, and crypto wallet files from 22 different browsers.
It went after Telegram and Discord credentials, too. The malware used the Discord API to slide into the DMs of its victims’ friends, propagating itself by doing so.
That’s not all; it infected VPNs too, and it targeted Mullvad, NordVPN, ExpressVPN, and ProtonVPN. And its modular setup made it so buyers had the ability to pick which features they preferred. Extra modules included a Chrome grabber, wallet patchers for Exodus and Atomic, screenshot tools, HVNC access, and stealers for FileZilla and Steam.
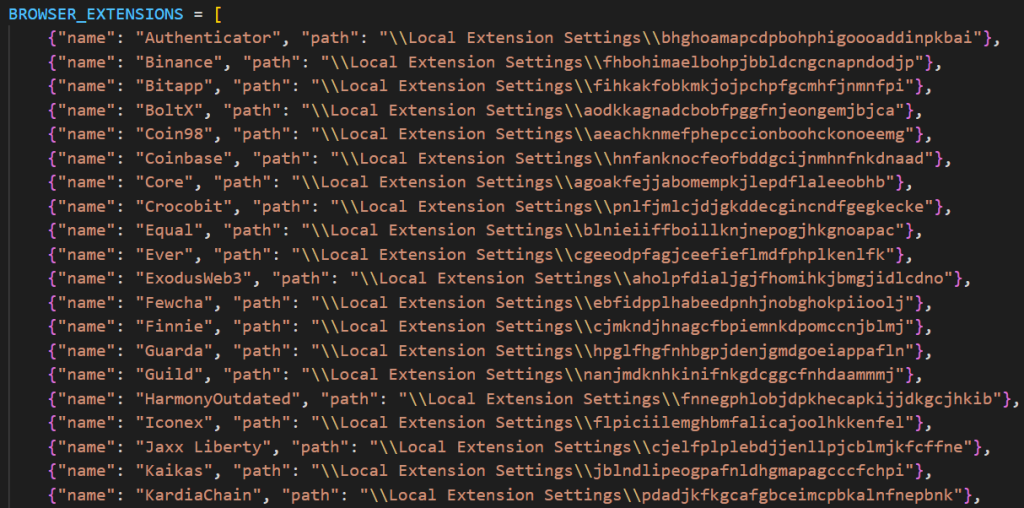
List of Targeted Cryptocurrency Extensions
Source by: Kaspersky
Premium Features for Bigger Targets
The C++ version stepped things up significantly. It added RDP credential theft, the ability to resist sandbox checks, and anti-debugging tricks to avoid analysis.
Gamers became prime targets. The premium variant went after accounts for Epic Games, Battle.net, Riot, Unreal Engine, Ubisoft Connect, and GOG.
The real kicker was ChromElevator. The malware injects this into the browser after suspending the browser processes to steal data. More importantly, it bypassed Google’s iApp-Bound Encryption protection. That’s the security feature meant to keep credentials safe even when malware gets on your system.
This focus on evading security measures is a growing trend just weeks ago, a new ‘CastleCrypt’ malware crypter emerged on hacking forums, claiming to bypass security using similar techniques to hide malicious payloads from antivirus and endpoint detection systems.
Why This Matters
Kaspersky pointed out something interesting. Arkanix felt more like a legitimate software product than typical shady stealer malware. The whole operation had a professional feel to it, from the two-tier pricing to the community management.
The researchers think projects like this make detection harder. When malware developers use AI to build things quickly and then disappear, security teams struggle to keep up.
Maybe the creator made some quick cash and moved on. Maybe they gathered data on how a tool developed using AI assistance performs in the real world. We might never know.
What we do know is that the indicators of compromise are out there now. Hashes, domains, IP addresses. Should Arkanix return, defenders will be prepared to fight it. But for us regular folks, the fact that Arkanix’s creator used help from AI to write it reminds us how smart cybercriminals are becoming.